CCNA Discovery 4 Module 4 Exam Answers Version 4.0
1. In addition to the technical considerations, what other major factor is used to evaluate the success of a network installation?
• final project costs
• maintenance costs
• user satisfaction
• statistics describing the performance of network devices
2. Which two network applications are most affected by network congestion and delays? (Choose two.)
• IP telephony
• live video webcasts
• audio file downloads
• online banking services
• file archival and retrieval
3. What two Cisco tools can be used to analyze network application traffic? (Choose two.)
• NBAR
• NetFlow
• AutoQoS
• Wireshark
• Custom Queuing
4. In network design, which technology can be implemented to prioritize traffic based on its importance and technical requirements?
• STP
• QoS
• RTP
• TCP
• VPN
5. What are two characteristics of voice over IP traffic? (Choose two.)
• Voice packets tend to be small.
• Voice packets must be processed in real time.
• Voice packets can effectively use TCP reliability features.
• Voice traffic can survive packet drops and retransmission delays.
• Voice packets must be converted to analog before being sent across the IP network.
• Voice packets automatically receive a higher priority value than other types of packets.
6. What are two things that a network designer can do to determine current and anticipated network traffic flows? (Choose two.)
• Survey end users to obtain customer input.
• Upgrade the Cisco IOS software in all networking devices to optimize traffic flow.
• Limit the analysis to host-to-server traffic because host-to-host traffic is unimportant.
• Run a network traffic analysis to determine which applications are in use and by whom.
• Conduct an inventory of all networking devices that includes model numbers and memory configurations
7. A company that has a traditional telephone system wants to convert to IP telephony. Which two factors should be considered for the design? (Choose two.)
• Digital communications systems have greater noise than analog systems when processing voice traffic.
• Voice-enabled routers or a server must be used for call control and signaling.
• Voice to IP conversions can cause router overhead.
• Power to the phones can be supplied through properly equipped patch panels or switches.
• The cost to combine voice and data VLANs can be a considerable amount.
8. Several web and email servers have recently been installed as part of an enterprise network. The security administrator has been asked to provide a summary of security features that can be implemented to help prevent unauthorized traffic from being sent into or out of sensitive internal networks. Which three features should the security administrator recommend? (Choose three.)
• firewalls
• priority queuing
• access control lists
• intrusion detection systems
• DHCP
• 128-bit WEP
9. The design of an IP telephony system needs to meet the technical requirements to provide a connection to the PSTN as well as provide high-quality voice transmissions using the campus network. Which two elements directly affect the ability of the design to meet these requirements?(Choose two.)
• voice-enabled firewall
• PoE switches and patch panels
• redundant backbone connectivity
• voice-enabled router at the enterprise edge
• separate voice and data VLANs with QoS implemented
10. When implementing VoIP services, which two design considerations should be followed?(Choose two.)
• Confirm that network jitter is minimal.
• Use TCP to reduce delays and dropped packets.
• Establish priority queuing to ensure that large data packets are sent uninterrupted.
• Disable real-time protocols to reduce queuing strategy demands.
• Ensure that packet delays do not exceed 150 ms.
11. What design strategy should be followed when designing a network that uses video on demand?
• implement the appropriate routing protocol to ensure that data segments arrive in order
• implement different QoS queues based on the type of video traffic being distributed
• install servers to store the data in a centrally located server farm
• configure queuing in the core routers to ensure high availability
12. When implementing QoS in traffic queues, what is the first step the designer should take to ensure that traffic is properly prioritized?
• define QoS policies
• define traffic classes
• determine traffic patterns
• identify traffic requirements
• identify networking equipment
13. Which two statements are characteristics of file transfer traffic flows? (Choose two.)
• RTP should be used.
• Traffic is predictable.
• Packets are small in size.
• Transfers are throughput intensive.
• Response-time requirements are low.
14. Which two items can be determined by diagramming internal traffic flow? (Choose two.)
• the type of ISP services needed
• the capabilities of end-user devices
• the areas where network congestion may occur
• the location of VPN servers used to connect teleworkers
• locations where high-bandwidth connections are required
15. Which two traffic types are examples of external traffic flows? (Choose two.)
• A user in the IT department telnets to the core layer router.
• A user in marketing connects to the web server of a competitor.
• A user in the IT department telnets into the access layer switch.
• A user in the services department logs in to a web-based email program.
• A user in accounting connects to an FTP server that is connected to the access layer switch.
16. Which service can be provided by the NetFlow Cisco utility?
• network planning and mapping
• IDS and IPS capabilities
• peak usage times and traffic routing
• network billing and accounting application
• security and user account restrictions
• source and destination UDP port mapping
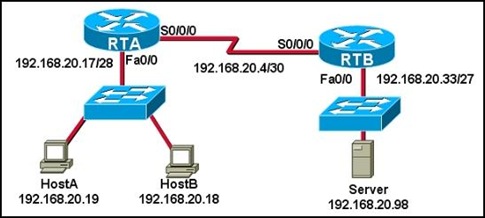
17. Refer to the exhibit. If ACL 150 identifies only voice traffic from network 192.168.10.0/24 and no other traffic, which queue will voice traffic from other networks use?
• high
• normal
• medium
• default
18. Refer to the exhibit. After configuring QoS, a network administrator issues the command show queueing interface s0/1. What two pieces of information can an administrator learn from the output of this command? (Choose two.)
• queue traffic definitions
• priority list protocol assignments
• type of queuing being implemented
• number of packets placed in each queue
• queuing defaults that have been changed
• queuing has not been applied to this interface
19. An analysis of network protocols reveals that RTP and RTCP are being used. What uses these protocols?
• IDS
• VPN
• WLAN
• firewall
• real-time video
20. A company is considering adding voice and video to the data networks. Which two statements are true if voice and video are added? (Choose two.)
• PoE switches must be purchased.
• More UDP-based traffic flows will be evident.
• Response times will be increased even if QoS is implemented.
• QoS will most likely be implemented to prioritize traffic flows.
• VPNs will most likely be implemented to protect the voice traffic.
21. Refer to the exhibit. Which option correctly matches the terms on top with its definition on the bottom?
• A=1, B=3, C=2, D=4
• A=2, B=1, C=4, D=3
• A=2, B=4, C=1, D=3
• A=3, B=2, C=4, D=1
• A=4, B=3, C=1, D=2
• A=4, B=2, C=3, D=1
22. A database server is configured to purge all data that is 60 days old. Ten data items that are 60 days old are to be purged. However, there is a failure halfway through the transaction, and the entire transaction is voided. What type of transaction action occurred?
• atomic
• consistent
• durable
• isolated
23. What is the primary goal of QoS?
• classification of traffic
• filtering and queuing voice traffic
• reducing bandwidth requirements
• providing priority service to selected traffic
24. Which technology provides a mechanism for implementing QoS at Layer 2?
• ToS
• CoS
• DSCP
• IP precedence
25. A customer purchases tickets online and pays using a credit card, but the system goes down before the transaction is complete. What transaction type retains a record of this transaction after the system failure so that the customer will still receive the tickets and the credit card account will be debited accordingly?
• atomic
• consistent
• durable
• isolated
26. Refer to the exhibit. The network design documents include requirements to prevent switching loops, to provide link-specific failover, and to provide Layer 3 recovery. Which two protocols would be needed to provide the support? (Choose two.)
• HDLC
• HSRP
• PPP
• RSTP
• VTP
27. network design must minimize latency to support real-time streaming applications. Which two protocols enable control and scalability of the network resources and minimize latency by incorporating QoS mechanisms? (Choose two.)
• RTCP
• HSRP
• RSTP
• RTP
• RPC
28. Which two major differences are associated with IP telephony when compared to traditional telephony that uses a PBX? (Choose two.)
• manages phones centrally
• utilizes centralized call routing
• creates peer-to-peer relationships between phones
• requires a separate infrastructure to support data transfer
• requires significant manual configuration when adding, moving, or changing phones
29. When QoS is implemented in a converged network, which two factors can be controlled to improve performance? (Choose two.)
• link speed
• delay
• packet routing
• jitter
• packet addressi
CCNA Discovery 4 Module 3 Exam Answers Version 4.0
1. It is important to identify the details of network sections and devices that will be affected or involved in a new design. This information is included in which section of the Network Design Requirements Document?
• Project Goal
• Project Scope
• Technical Requirements
• Current State of the Network
2. Which two pieces of information does the network designer need to determine if the Cisco IOS of a router requires an upgrade? (Choose two.)
• amount of NVRAM installed
• model number of the router
• number of interfaces and installed HWICs
• installed Cisco IOS feature set and version
• error statistics for each interface
3. Which three pieces of information need to be considered when selecting the proper Cisco IOS version for an upgrade? (Choose three.)
• processor ID
• interface type
• amount of DRAM
• bootstrap version
• device make and model
• size of system flash memory
4. What are two practices a network technician should follow when installing a new interface card in a router? (Choose two.)
• Be sure the interface card faceplate does not touch the chassis rear panel.
• Do not tighten the captive screws until the router has been powered on and recognizes the card.
• Store the blank faceplate inside the card slot to be used if the card is removed.
• Handle the interface card by the edges to avoid static discharge.
• Push the interface card into place until the edge connector is seated securely
5. The new serial interface card for the router arrives and the network technician reads that it is hotswappable. What does this mean?
• The card cannot be installed while the router is powered on because static discharge could damage the card.
• The card cannot be installed until the router is powered off and completely cooled down.
• The card can be installed while the router is powered on if the router supports this technology.
• The card is a replacement and must be installed in the same slot as the card it is replacing.
6. Refer to the exhibit. A network administrator issues the command shown to gain knowledge about a poorly documented network. Which two pieces of information can the network administrator discover from the command output? (Choose two.)
• One connected device has router capability.
• The entire network contains a total of five Cisco devices with CDP enabled.
• None of the directly connected network devices have been configured with an IP address.
• Device EDGE_2811 is connected to port Fast Ethernet 0/0 on device C3750-24_MDF.
• Five Cisco devices with CDP enabled are directly connected to device C3750-24_MDF
7. Refer to the exhibit. Which of the three Cisco IOS images shown will load into RAM?
• The router selects an image depending on the value of the configuration register.
• The router selects the third Cisco IOS image because it is the most recent IOS image.
• The router selects the second Cisco IOS image because it is the smallest IOS image.
• The router selects an image depending on the boot system command in the configuration.
• The router selects the third Cisco IOS image because it contains the advipservicesk9 image.
8. An administrator wants to download a new Cisco IOS software version to the local router. Which command performs this task?
• copy tftp flash
• copy flash run
• copy start tftp
• copy flash tftp
• copy tftp start
9. Refer to the exhibit. The top of the output shows the Cisco Feature Navigator regarding a Cisco IOS image that the administrator wants to install on a router. Below it is the output from the show version command for that router. Which statement is true regarding the capacity of the router to run this Cisco IOS image?
• There is not enough DRAM and flash.
• There is enough DRAM and flash.
• There is enough DRAM but not enough flash.
• There is enough flash but not enough DRAM.
10. Which two items are objectives of a WLAN design site survey? (Choose two.)
• identify coverage areas
• determine primary AP locations
• determine what AP equipment should be purchased
• determine how many users will access the WLAN
• identify the bottleneck of the LAN infrastructure
11. Refer to the exhibit. Which two actions improve the weaknesses of the topology shown, assuming that each access layer segment is in its own subnet? (Choose two.)
• Implement redundant links to each server by adding additional NICs.
• Implement a reduntant link from all access layer switches to Admin, Dist, and Server Farm.
• Implement a backup firewall with a link to a secondary ISP and implement a redundant link to the DMZ.
• Implement reduntant links from the existing firewall to all access layer switches.
• Implement redundant links from the DMZ to Admin and Dist.
12. A company is beginning to analyze their new Cisco IOS upgrade requirements. What is one of the router components that a network administrator must consider when selecting a new Cisco IOS version?
• processor type
• storage space in NVRAM
• interfaces and modules to be supported
• compatibility of the bootstrap version with the new Cisco IOS software
13. An employee at a company notices that the wireless signal strength indicator on his laptop fluctuates from good to low. The network administrator decides to do a site survey of that area. Which three factors need to be included in the survey? (Choose three.)
• type and model number of the WNIC of the laptop
• number of users in the area
• location of the AP
• list of MAC addresses filtered by the AP
• number of simultaneous applications running on the laptop of the employee
• location of walls and filing cabinets in the office
14. The new network design for AnyCompany must include support of voice and video traffic. Before upgrading, the network designer checks whether the existing devices can support the new requirements. Which three items does the designer need to check? (Choose three.)
• number of routers and switches owned by AnyCompany
• routers that will support extra ASICs and WWICs
• size of DRAM and flash on each device
• routers that will support HWICs and VWICs
• system bootstrap version on each router and switch
• modules supported on the loaded Cisco IOS
15. A new Cisco IOS version has been copied into flash from a TFTP server. When a reload is issued to upgrade the Cisco IOS, the router freezes part of the way through the loading process. What could be the problem?
• There is enough flash but not enough RAM in the router.
• The new HWIC cards have not been installed yet.
• The TFTP server needs to be present during a reload.
• The new Cisco IOS should have been loaded into NVRAM.
• The new bootstrap version is not compatible with the original version on the router.
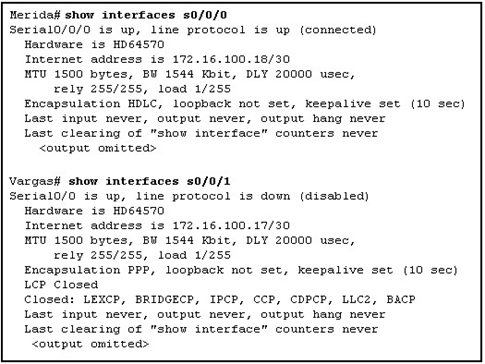
16. Refer to the exhibit. A network designer has no documentation and is attempting to create a logical diagram of the network using the output from show commands. What can be determined from the output shown?
• The device with the ID of ISP is a router on the Internet.
• The attached switch is a VTP server in the Toronto domain.
• The designer cannot telnet to the attached switch.
• The Cisco router IOS supports enterprise-level voice and video technologies.
17. A production router is reloaded and finishes with a Router> prompt. What three facts can be determined? (Choose three.)
• POST occurred normally.
• The boot process was interrupted.
• There is not enough RAM or flash on this router.
• A full version of the Cisco IOS was located and loaded.
• A configuration file was not located in NVRAM or from a TFTP server.
• The router did not locate the Cisco IOS in flash, so it defaulted to ROM.
18. During a site survey, the network designer noticed that people were accessing the company wireless network from the parking lot. What should be done to stop the wireless signal from radiating out into the parking lot?
• change the channel on the wireless AP
• connect the wireless AP to a firewall
• change the type of antenna attached to the AP
• move the wireless AP to a secure VLAN
• move the wireless AP to a port on a Layer 3 switch
19. A network design project includes a review of the existing network. What is the purpose of this phase of the project?
• eliminate the need for a site survey
• shorten the timeframe of the project
• lower the cost of the project by removing redundant links and devices
• determine if the number of applications used within the company can be reduced
• To determine what existing network devices require upgrades to meet the new
20. Refer to the exhibit. Based upon the Cisco IOS file naming convention, what is represented by the value ipvoicek9 listed in the IOS filename?
• version
• file format
• feature set
• hardware platform
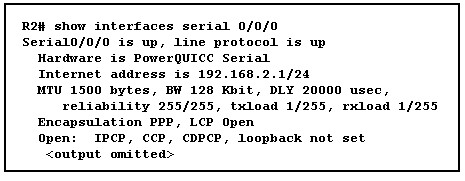
21. Refer to the exhibit. What two items can be determined from the output? (Choose two.)
• R2 is a Cisco 2600 device.
• R2 has 22 MB of RAM installed.
• The version of the IOS is 12.3.
• Over 8 MB of NVRAM is installed.
• A new 36 MB IOS file can be installed on the device.
22. During a wireless site survey, a consultant is determining the hours of peak usage and the estimated number of users in each location. The consultant is currently in what step of the site survey process?
• the defining of customer requirements
• the identification of coverage areas
• the determining of preliminary AP locations
• the measurement of signal strength
23. Refer to the exhibit. The network administrator is attempting to install a new version of the IOS on R2. Based on the exhibited output, what are two possible reasons that the transfer failed?(Choose two.)
• The administrator did not enable TFTP on R2.
• There is not enough flash available to store the new IOS.
• Connectivity between R2 and the TFTP server was not verified.
• The copy command was incorrectly entered.
• The administrator did not verify that the TFTP server is running.
24. In which section of the Network Design Requirements document would a network consulting team detail names and IP addresses of important networking components and servers, provide network diagrams and topologies, and define strengths and weaknesses of the network?
• network requirements
• project scope
• overall project goal
• state of the network
CCNA Discovery 4 Module 2 Exam Answers Version 4.0
1. During an evaluation of the currently installed network, the IT staff performs a gap analysis to determine whether the existing network infrastructure can support the desired new features. At which stage of the Cisco Lifecycle Services approach does this activity occur?
• Prepare Phase
• Plan Phase
• Design Phase
• Implement Phase
• Operate Phase
• Optimize Phase
2. Which stage of the Cisco Lifecycle Services strategy is usually completed before an organization issues a Request For Proposal (RFP) or Request For Quotation (RFQ)?
• Prepare Phase
• Plan Phase
• Design Phase
• Implement Phase
• Operate Phase
• Optimize Phase
3. What is the purpose of SNMP?
• to facilitate the exchange of information between devices and the NMS
• to monitor and control managed network devices
• to report user logins to a monitoring station
• to verify traffic throughout the network and keep a log of all activity
4. During an analysis of a customer network, several possible opportunities for network improvement are identified. At which stage of the Cisco Lifecycle Services does this process occur?
• Prepare Phase
• Plan Phase
• Design Phase
• Implement Phase
• Optimize Phase
• Operate Phase
5. What provides the initial data for the Optimize Phase?
• performance monitoring
• business goals
• technical goals
• RFP
6. Which two statements are true regarding the response to an RFQ?(Choose two.)
• The response should be brief.
• it should strictly conform to the formatting requirements specified by the RFQ.
• Only the items that the contracting company will be addressing should be answered.
• The response helps the customer compare pricing with other potential contractors.
• The response is more complicated than a response to a RFP.
7. What are two disadvantages of using a bottom-up approach instead of a top-down approach to network design? (Choose two.)
• It can result in an inappropriate network design.
• A new design cannot be implemented right away.
• It does not take into account the business goals of the company.
• This approach is not commonly practiced and is therefore not as well known.
• It requires tedious and time-consuming meetings with the customer to develop an understanding of the organization.
8. What is a business constraint that may impact the WAN design of a company?
• company policy regarding specific operating systems on LAN devices
• current monitoring protocols implemented on end-user devices
• non-availability of end users during implementation
• company policy requiring the use of specific vendor networking equipment due to partnerships
9. What is the purpose of preparing a business case?
• to justify the financial investment in implementing the technology change
• to provide an example of a previous job done in the RFP
• to define the technical requirements of the network
• to define timelines and critical milestones
10. What is the purpose of creating a prioritized list of technical requirements?
• defines the project scope
• determines the business profitability
• creates a feasibility report for analysis
• identifies existing and new user groups
11. A network engineer is analyzing the network of a potential client company to identify problems and determine whether a network upgrade or addition is needed. Which role in the sales team is this engineer assuming?
• post-sales field engineer
• pre-sales engineer
• account manager
• network designer
12. Which two statements best describe the responsibilities of an account manager? (Choose two.)
• acts as the primary point of contact between the company and the client
• directs the sales teams and support personnel
• provides technical support to critical clients
• selects the equipment and technologies to be used for the client solution
• acts as the network design lead
13. What is the purpose of system-level acceptance testing?
• To develop an installation plan for the newly designed network
• to train end users and support personnel on the newly installed network
• to check that the newly installed network meets the business goals and design requirements
• to justify the financial investment required to implement the technology change
14. What is a purpose of establishing a network baseline?
• It provides a statistical average for network performance.
• It manages the performance of network devices.
• It creates a point of reference for future network evaluations.
• It checks the security configuration of network devices.
15. When should a network baseline be performed within the stages of the Cisco Lifecycle Services?
• Prepare Phase
• Plan Phase
• Design Phase
• Implement Phase
• Operate Phase
16. What are two benefits of using a top-down approach instead of a bottom-up approach to network design? (Choose two.)
• incorporates organizational requirements
• allows for a quick response to a design request
• requires less time up front to create a network design
• clarifies design goals from the perspective of applications and network solutions
• facilitates a design by using devices and technologies that are based on previous experience
17. Which software component is installed on network devices that are managed through SNMP?
• management agents
• management stations
• network management protocol
• Management Information Base (MIB)
18. A network engineer working for a contracting company is informed of a pre-bid meeting with a potential client. What purpose does the network engineer have for attending the pre-bid meeting?
• to submit request for proposal responses
• to discuss proposed installation and monitoring plans
• to perform system-level acceptance tests on the current network
• to clarify project scope and timelines not included in the original request for proposal
• to create a business case outlining reasons for financial investment in a network upgrade
19. A major corporation has decided to hire someone to upgrade their network infrastructure. A network consulting company wants the job. What document must the network consulting company obtain to learn about the business goals, the project scope, the requirements for the new network and the expected deliverables?
• Business Case
• Project Plan
• Request for Proposal
• Request for Comments
20. A corporation (client) wants a network upgrade and is putting out a request for services to various network consulting companies (contractors). A RFQ is required. Which statement is true concerning the RFQ?
• sent from the contractors to the client in response to a RFP
• sent from the client to the contractors along with the RFP to provide more specific technical details
• sent from the client to the contractors in place of a RFP when the technical specifications of a project are known
• sent from the contractors to the client outlining reasons for financial investments for the network upgrade
21. Which stage of the Cisco Lifecycle Services involves proactive management to identify and resolve issues before the organization is affected?
• Prepare Phase
• Plan Phase
• Design Phase
• Implement Phase
• Operate Phase
• Optimize Phase
22. Why is it important to prioritize business goals when developing network design?
• to ensure that the least expensive technologies are implemented first
• to simplify the configuration, administration, and monitoring of the newly installed network
• to anticipate the effects of changes and growth of the business
• to adhere to the best opportunities to contribute to the success of the business
23. Which two items help identify business goals and priorities before a new network project starts? (Choose two.)
• installation
• motivation
• profitability
• trustworthiness
• customer satisfaction
24. A network engineer working for ABC company is writing a response to an RFP for a network upgrade and must create an executive summary. Which statement describes the basic components of an executive summary?
• quick overview of the problem, the recommended solution, and the justification for ABC company doing the job
• detailed description of the solution, including but not limited to, timelines, turnover schedule, warranty information, and emergency recovery information
• detailed description of costs including, the cost of software and hardware components, licensing requirements, labor cost, and other applicable fees
• multiple page document containing additional information such as detailed lists of equipment required, diagrams, company background information, and insurance coverage
25. In a network management architecture, which statement best describes a management agent?
• communication protocol used between a management station and managed device
• standardized database that a device keeps about itself concerning network performance parameters
• host with the management application loaded that is used by the administrator to monitor and configure network devices
• software running on a managed device to collect network information and allow that device to be managed by a management station
CCNA Discovery 3 Module 9 Exam Answers
Version 4.0
1.
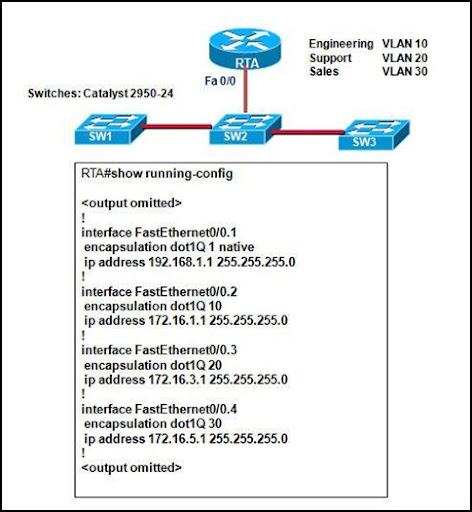
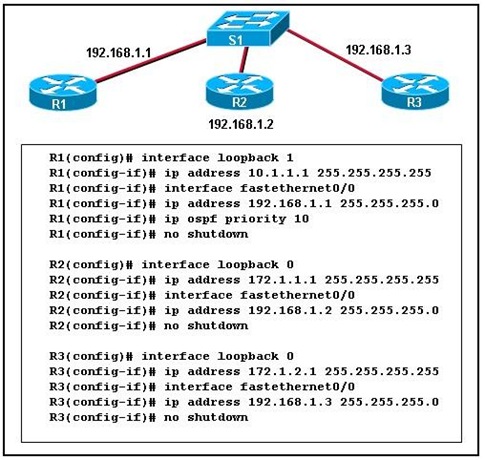
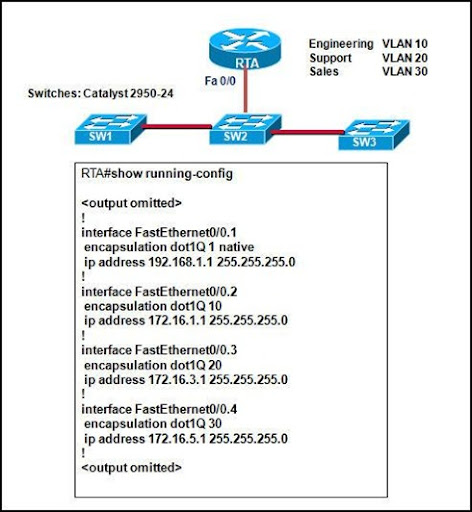
Refer to the exhibit. Based on the output shown, to which IP network should the workstations in the Support department belong?
• 192.168.1.0
• 172.16.1.0
• 172.16.3.0
• 172.16.5.0
2.
Refer to the exhibit. A network administrator is doing proactive network maintenance. The administrator pings 192.168.1.100 and compares the results to the baseline data. Based on the comparison of the two pings, what is one possibility?
• There is an ACL applied, making the destination host unreachable.
• There is a malfunctioning NIC on the destination host.
• The sending host is unable to access the network.
• There are congestion problems on the network.
3.
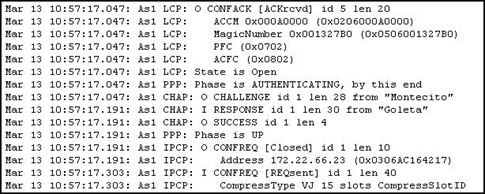
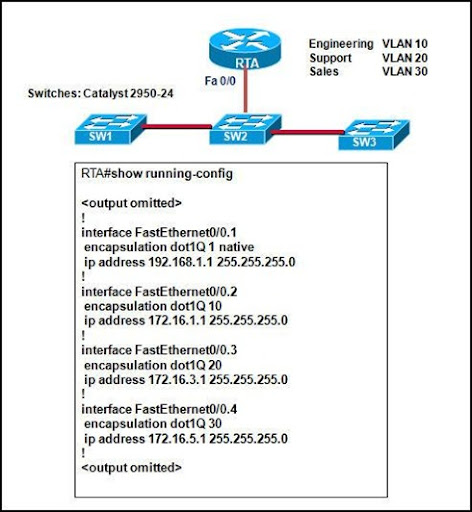
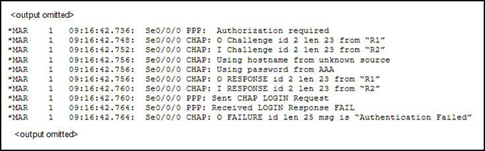
Refer to the exhibit. Given the output generated by the debug ppp negotiation command, which statement is true?
• The line protocol of the local router is now up.
• The username ’Goleta’ is configured locally.
• The command ppp authentication pap is configured on both routers.
• The local router requested to terminate the session.
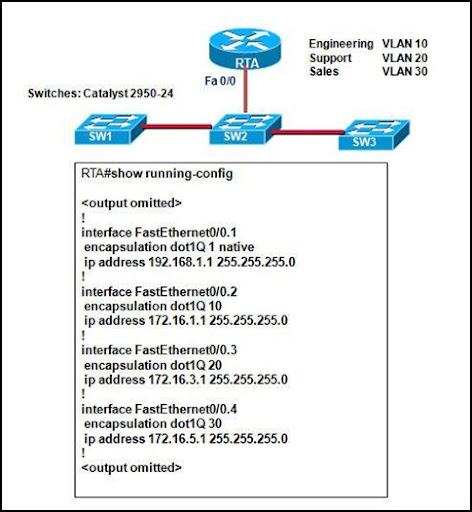
4. What is important to consider while configuring the subinterfaces of a router when implementing inter-VLAN routing?
• The subinterface numbers must match the VLAN ID number.
• The physical interface must have an IP address configured.
• The IP address of each subinterface must be the default gateway address for each VLAN subnet.
• The no shutdown command must be given on each subinterface.
5.
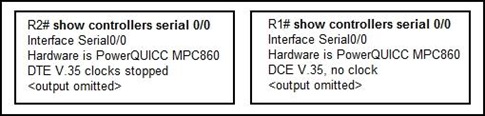
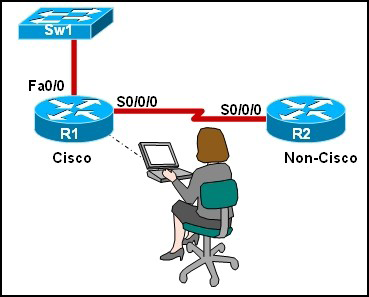
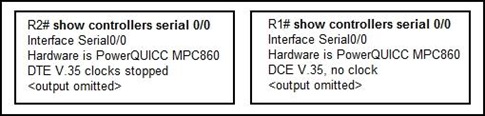
Refer to the exhibit. A lab technician connects two routers together via a serial cable using the default interface configuration values. The interfaces are up; however, the technician is unable to ping between the two devices. What is the most likely problem?
• The lab technician used the wrong cable to connect the serial ports.
• There is an IP mismatch between the serial ports.
• There is an encapsulation mismatch between the serial ports.
• No clock rate has been set on the DCE interface.
6.
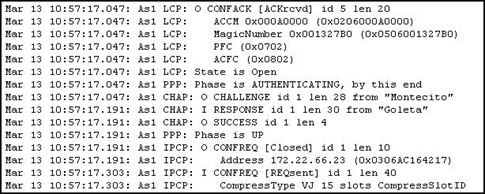
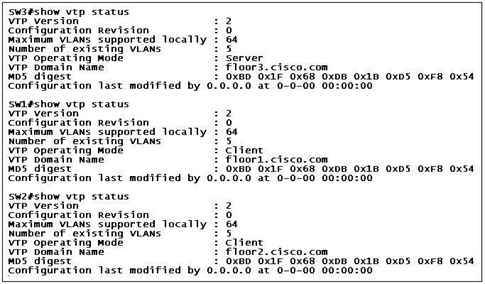
Refer to the exhibit. Based on the output shown, why is VTP information unable to propagate the network?
• One of the two client mode switches must be reconfigured to Transparent mode.
• Each switch must be synchronized to the network time server.
• The VTP domain names are different.
• VTP passwords must be set.
• The configuration revision numbers are all the same.
7. The enterprise mail server software recently went through a minor update. A network administrator notices an excessive amount of traffic between a database server and the newly updated mail server, compared to the baseline data. What is the first action the administrator should do to investigate the problem?
• Wait to see if the recent update will stabilize after a while.
• Redo the baseline data to include the minor upgrade.
• Check the log to see what software components are producing the excess traffic.
• Check for viruses and spyware on the database server.
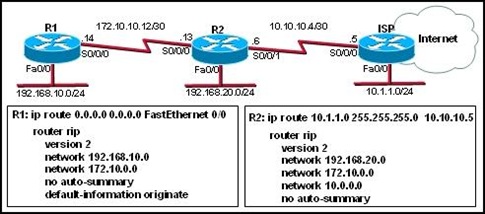
8.
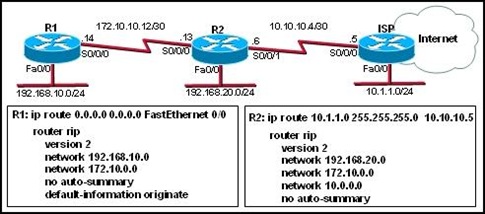
Refer to the exhibit. Users are reporting that they cannot access the Internet. Routers R1 and R2 are configured with RIP version 2 as shown. If R2 receives a packet with a destination address on the Internet, how is the packet routed?
• The packet is routed to the ISP router and then to network 10.1.1.0/24.
• The packet is routed to the ISP router and then to the Internet.
• The packet is routed to R1 and then forwarded out Fa0/0 on R1.
• The packet will not be routed because R2 does not have a valid default route.
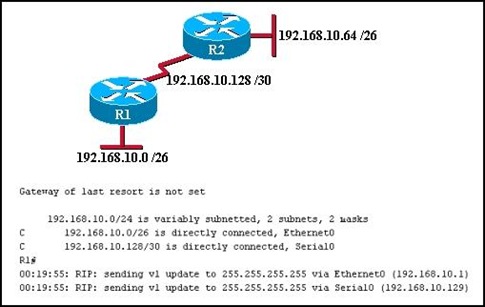
9.
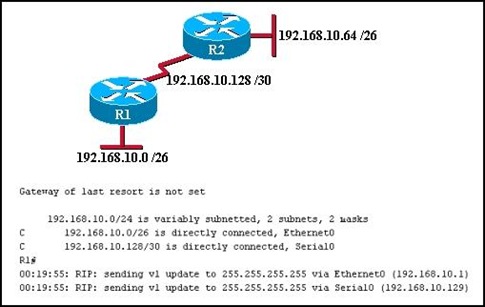
Refer to the exhibit. Both routers are configured using RIPv1. Both routers are sending updates about the directly connected routes. R1 can successfully ping the serial interface of R2. The routing table on R1 does not contain any dynamically learned routes from R2, and the routing table on R2 shows no dynamically learned routes from R1. What is the problem?
• Subnetting is not supported by RIPv1.
• One of the routers needs a clock rate on the serial interface.
• The serial link between the two routers is unstable.
• VLSM is not supported by RIPv1.
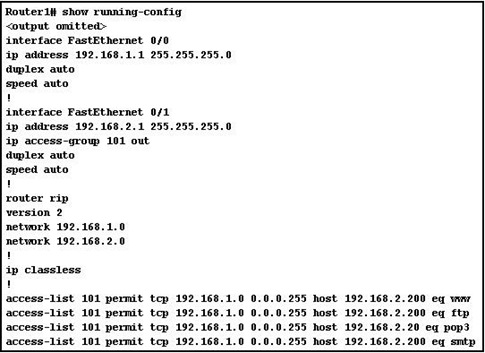
10.
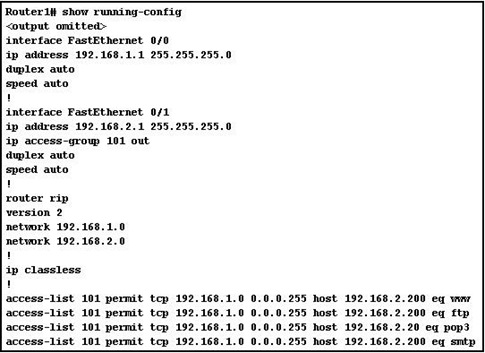
Refer to the exhibit. Host 192.168.1.14 is unable to download email from 192.168.2.200. After reviewing the output of the show running-config command, what problem is discovered?
• Access to the SMTP server is denied.
• The destination host address in an ACL statement is incorrect.
• The ACL is applied to the interface in the wrong direction.
• The implicit deny any any is blocking all access to email.
11. An employee called the help desk to report a laptop that could not access a web-based application on the Internet. The help desk technician asked the employee to open a Windows command prompt and type the ipconfig /all command. Which problem-solving technique did the technician choose?
• top-down
• bottom-up
• substitution
• divide-and-conquer
12.
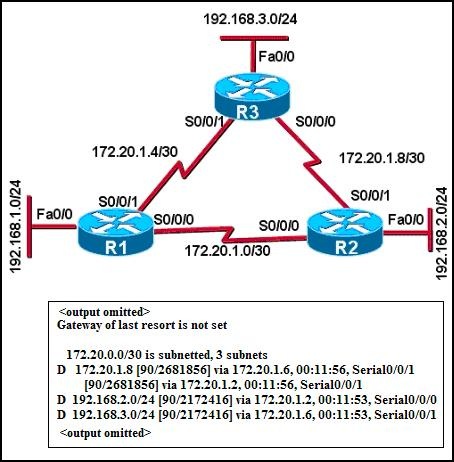
Refer to the exhibit. Based on the network diagram and the output shown, which statement is true?
• The command was entered on router R1.
• The command was entered on router R2.
• The command was entered on router R3.
• The command could have been entered on either R1 or R2.
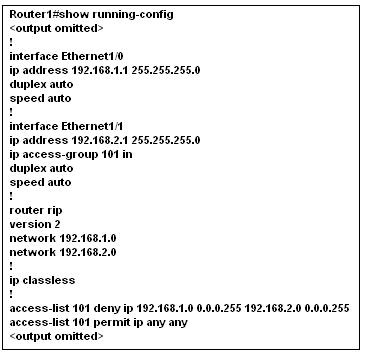
13.
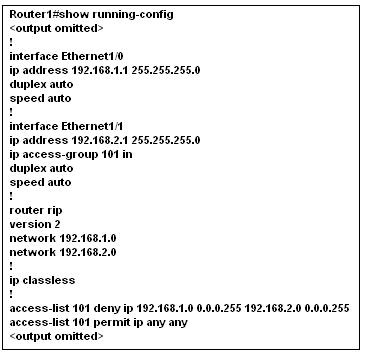
Refer to the exhibit. An ACL is configured to prevent access by network 192.168.1.0 to network 192.168.2.0, but it is not working properly. What problem is discovered after observing the output of the show running-config command?
• The protocol type specified in the ACL should be TCP, not IP.
• The source and destination addresses are reversed in the statement.
• The ACL is applied to the wrong interface, but the right direction.
• The ACL is applied to the wrong interface and the wrong direction.
• The permit ip any any statement allows network 192.168.1.0 access.
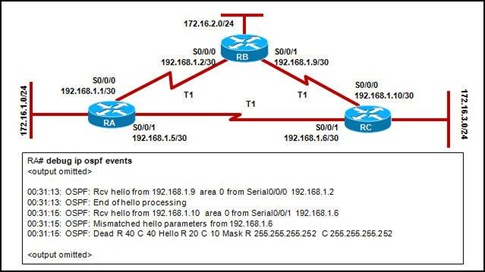
14.
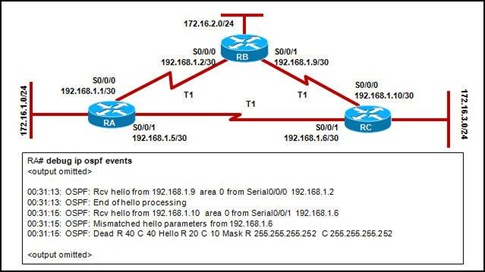
Although all networks are reachable, the network administrator notices abnormal routing behavior after configuring OSPF on each router. According to the partial output from the debug ip ospf events command, which statement is true about the contents of the routing table in RA?
• It will show network 172.16.3.0 learned from RB.
• It will show network 172.16.3.0 learned from RC.
• It will show two equal routes to network 192.168.1.4/30.
• It will show two equal routes to network 192.168.1.8/30.
15. A network at a large building failed, causing a severe disruption in business activities. The problem was eventually detected and resolved by replacing a piece of failed network equipment. Investigation led to the conclusion that a network design problem was the main cause of the disruption. Loss of a single piece of equipment should not have been able to cause such a large problem. What two terms best describe this type of design weakness? (Choose two.)
• bottleneck
• limited availability
• limited scalability
• large failure domain
• single point of failure
• limited staff capabilities
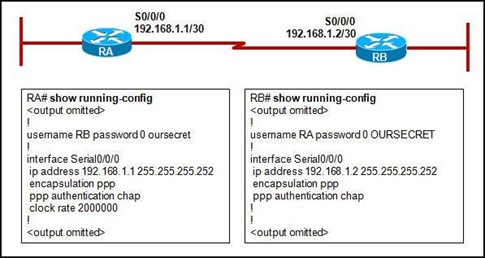
16.
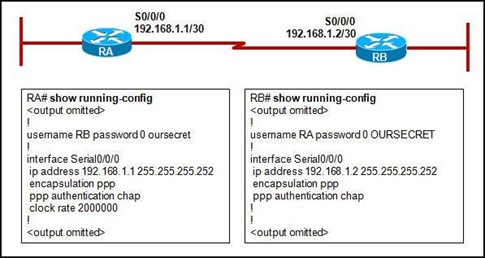
Refer to the exhibit. The network administrator is troubleshooting the connectivity issue between RA and RB. According to the partial configuration, what is the cause of the problem?
• password mismatch for PPP authentication
• username mismatch for PPP authentication
• encapsulation method mismatch for PPP authentication
• authentication method mismatch for PPP authentication
17.
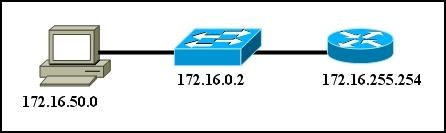
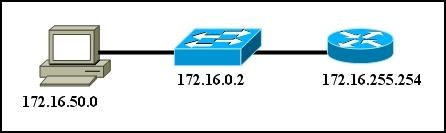
Refer to the exhibit. ABC Company is using the 172.16.0.0/18 network. It is standard company practice to use the first 50 addresses for switches and servers and assign the last usable address to the router. The remaining addresses are assigned to the hosts. After assigning the addresses, the network technician tests connectivity from the host above and is not able to ping the router. What could be the problem?
• The router was assigned the broadcast address.
• The host is not in the same subnet as the switch and router.
• The router interface is in the wrong subnet.
• The host was assigned a network address.
18.
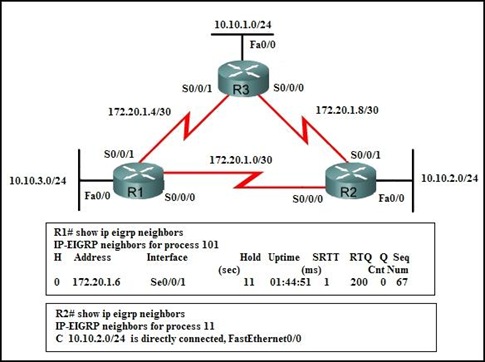
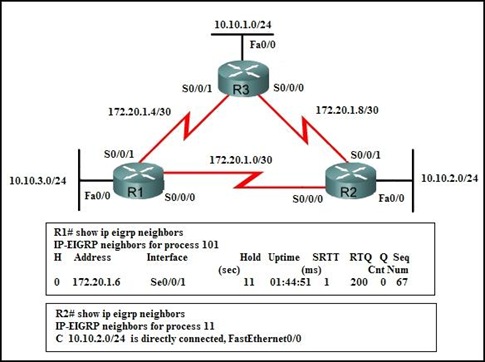
Refer to the exhibit. A network administrator is troubleshooting a problem. No users are able to access the 10.10.2.0/24 network, but are able to access all other networks. Assuming R3 is configured correctly and based on the output shown, what is most likely the problem?
• There is congestion on the 10.10.2.0 network.
• The EIGRP process number on R2 is incorrect.
• The Fa0/0 interface on R2 is shut down.
• The Fa0/0 interface on R2 has an incorrect IP address or subnet mask.
19.
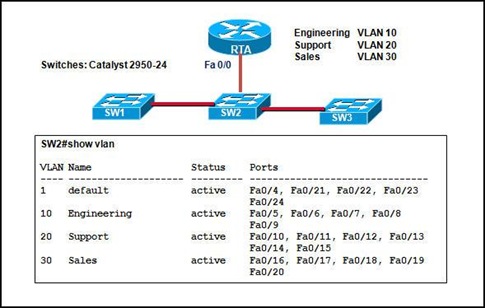
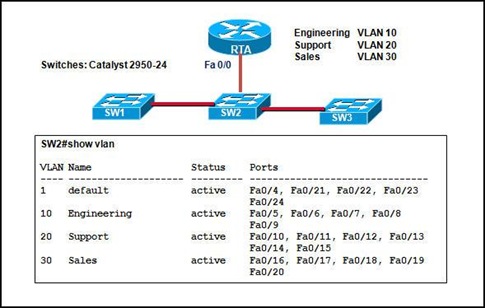
Refer to the exhibit. The network administrator correctly configures RTA to perform inter-VLAN routing. Using the show vlan command, the administrator verifies that port Fast Ethernet 0/4 is the first available port in the default VLAN on SW2. The administrator connects RTA to port 0/4 on SW2, but inter-VLAN routing does not work. What could be the possible cause of the problem with the SW2 configuration?
• Port 0/4 is not active.
• Port 0/4 must be a member of VLAN1.
• Port 0/4 is configured in access mode.
• Port 0/4 is configured as a trunk port.
20.
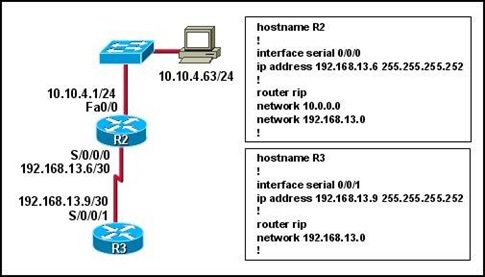
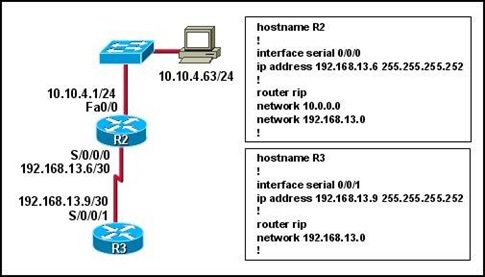
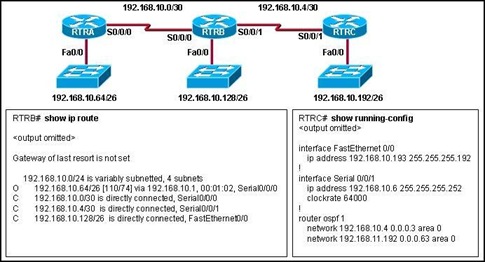
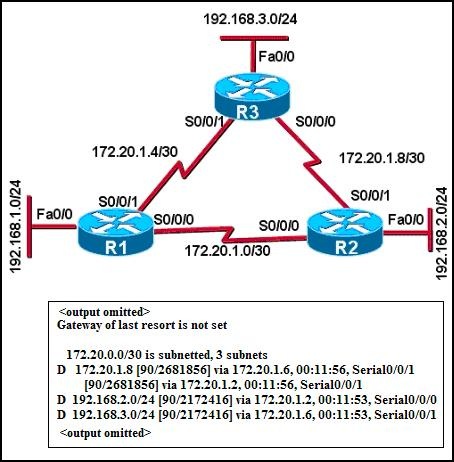
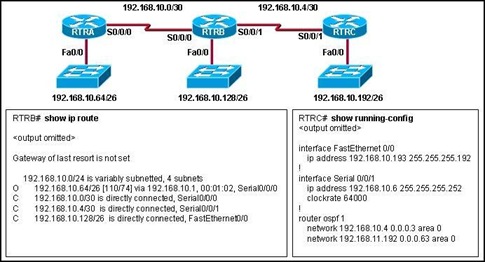
Refer to the exhibit. The network administrator is unable to ping from the console of router R3 to host 10.10.4.63. What is the problem?
• RIPv1 does not support VLSM.
• Router R2 does not have RIP correctly configured.
• Router R3 is missing a network statement for network 10.0.0.0.
• There is an addressing problem on the link between routers R2 and R3.
21.
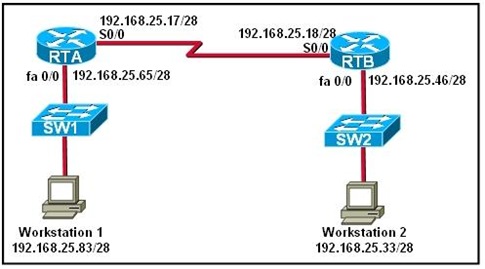
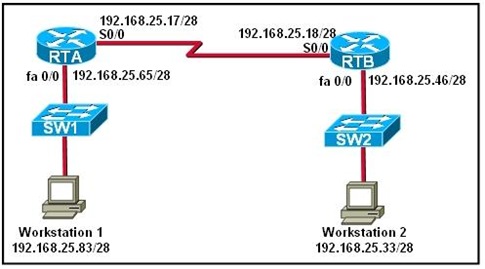
Refer to the exhibit. A network administrator has implemented subnetting using the network 192.168.25.0 and a /28 mask. Workstation 1 is not able to ping with Workstation 2. What is a possible cause for this lack of communication?
• Workstation 1 and Workstation 2 are on the same subnet.
• The serial connections are using addresses from the LAN subnets.
• All hosts in the network must be in the same subnet to communicate.
• Workstation 1 is not on the same network that the RTA router LAN interface is on.
22. Which two statements describe when a network administrator should perform a network baseline? (Choose two.)
• It should be done monthly as a minimum standard.
• It should be performed when all switch Cisco IOS versions are upgraded.
• It should be done when all network printers are upgraded to a new model.
• It should be done when the network is performing at normal activity levels.
• It should be done whenever an SLA has been signed with a new service provider.
CCNA Discovery 3 Module 8 Exam Answers Version 4.0
1.
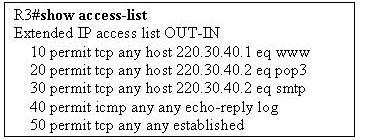
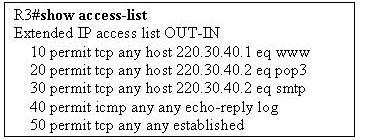
Refer to the exhibit. A network administrator needs to add the command deny ip 10.0.0.0 0.255.255.255 any log to R3. After adding the command, the administrator verifies the change using the show access-list command. What sequence number does the new entry have?
• 0
• 10, and all other items are shifted down to the next sequence number
• 50
• 60
2.
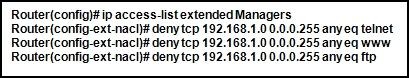
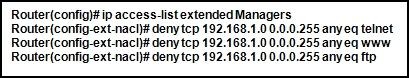
Refer to the exhibit. What happens if the network administrator issues the commands shown when an ACL called Managers already exists on the router?
• The new commands overwrite the current Managers ACL.
• The new commands are added to the end of the current Managers ACL.
• The new commands are added to the beginning of the current Managers ACL.
• An error appears stating that the ACL already exists.
3. Why are inbound ACLs more efficient for the router than outbound ACLs?
• Inbound ACLs deny packets before routing lookups are required.
• Inbound ACL operation requires less network bandwidth than outbound.
• Inbound ACLs permit or deny packets to LANs, which are typically more efficient than WANs.
• Inbound ACLs are applied to Ethernet interfaces, while outbound ACLs are applied to slower serial interfaces.
4.
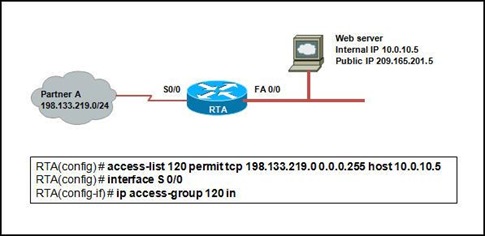
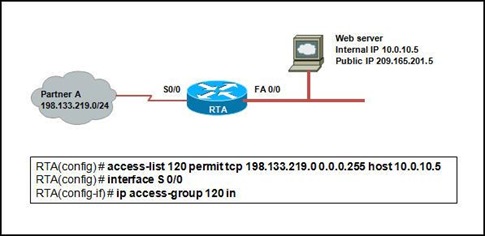
Refer to the exhibit. The network administrator of a company needs to configure the router RTA to allow its business partner (Partner A) to access the web server located in the internal network. The web server is assigned a private IP address, and a static NAT is configured on the router for its public IP address. Finally, the administrator adds the ACL. However, Partner A is denied access to the web server. What is the cause of the problem?
• Port 80 should be specified in the ACL.
• The public IP address of the server, 209.165.201.5, should be specified as the destination.
• The ACL should be applied on the s0/0 outbound interface.
• The source address should be specified as 198.133.219.0 255.255.255.0 in the ACL.
5. ACL logging generates what type of syslog message?
• unstable network
• warning
• informational
• critical situation
6. Which two host addresses are included in the range specified by 172.16.31.64 0.0.0.31? (Choose two.)
• 172.16.31.64
• 172.16.31.77
• 172.16.31.78
• 172.16.31.95
• 172.16.31.96
7. Traffic from the 64.104.48.0 to 64.104.63.255 range must be denied access to the network. What wildcard mask would the network administrator configure in the access list to cover this range?
• 0.0.15.255
• 0.0.47.255
• 0.0.63.255
• 255.255.240.0
8. ACLs are used primarily to filter traffic. What are two additional uses of ACLs? (Choose two.)
• specifying source addresses for authentication
• specifying internal hosts for NAT
• identifying traffic for QoS
• reorganizing traffic into VLANs
• filtering VTP packets
9. What can an administrator do to ensure that ICMP DoS attacks from the outside are mitigated as much as possible, without hampering connectivity tests initiated from the inside out?
• Create an access list permitting only echo reply and destination unreachable packets from the outside.
• Create an access list denying all ICMP traffic coming from the outside.
• Permit ICMP traffic from only known external sources.
• Create an access list with the established keyword at the end of the line.
10. What effect does the command reload in 30 have when entered into a router?
• If a router process freezes, the router reloads automatically.
• If a packet from a denied source attempts to enter an interface where an ACL is applied, the router reloads in 30 minutes.
• If a remote connection lasts for longer than 30 minutes, the router forces the remote user off.
• A router automatically reloads in 30 minutes.
11.
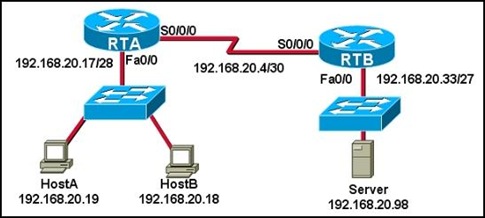
Refer to the exhibit. The following commands were entered on RTB.
RTB(config)# access-list 4 deny 192.168.20.16 0.0.0.15
RTB(config)# access-list 4 permit any
RTB(config)# interface serial 0/0/0
RTB(config-if)# ip access-group 4 in
Which addresses do these commands block access to RTB?
• 192.168.20.17 to 192.168.20.31
• 192.168.20.16 to 192.168.20.31*
• 192.168.20.16 to 192.168.20.32
• 192.168.20.16 to 192.168.20.33
12.
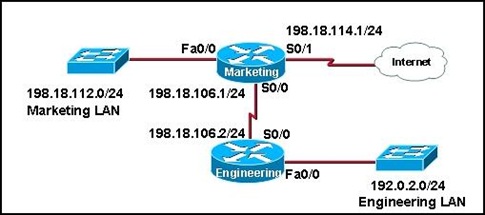
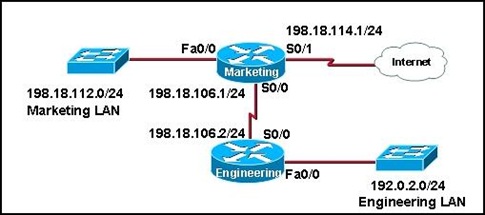
Refer to the exhibit. The new security policy for the company allows all IP traffic from the Engineering LAN to the Internet while only web traffic from the Marketing LAN is allowed to the Internet. Which ACL can be applied in the outbound direction of Serial 0/1 on the Marketing router to implement the new security policy?
• access-list 197 permit ip 192.0.2.0 0.0.0.255 any
access-list 197 permit ip 198.18.112.0 0.0.0.255 any eq www
• access-list 165 permit ip 192.0.2.0 0.0.0.255 any
access-list 165 permit tcp 198.18.112.0 0.0.0.255 any eq www
access-list 165 permit ip any any
• access-list 137 permit ip 192.0.2.0 0.0.0.255 any
access-list 137 permit tcp 198.18.112.0 0.0.0.255 any eq www
• access-list 89 permit 192.0.2.0 0.0.0.255 any
access-list 89 permit tcp 198.18.112.0 0.0.0.255 any eq www
13. Which three statements are true concerning standard and extended ACLs? (Choose three.)
• Extended ACLs are usually placed so that all packets go through the network and are filtered at the destination.
• Standard ACLs are usually placed so that all packets go through the network and are filtered at the destination.
• Extended ACLs filter based on source address only, and must be placed near the destination if other traffic is to flow.
• Standard ACLs filter based on source address only, and must be placed near the destination if other traffic is to flow.
• Extended ACLs filter with many possible factors, and they allow only desired packets to pass through the network if placed near the source.
• Standard ACLs filter with many possible factors, and they allow only desired packets to pass through the network if placed near the source.
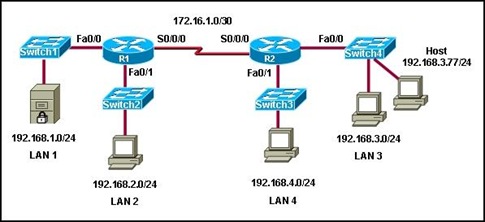
14.
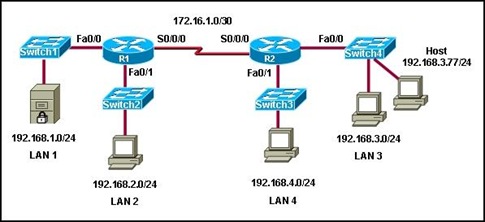
Refer to the exhibit. Company policy for the network that is shown indicates the following guidelines:
1) All hosts on the 192.168.3.0/24 network, except host 192.168.3.77, should be able to reach the 192.168.2.0/24 network.
2) All hosts on the 192.168.3.0/24 network should be able to reach the 192.168.1.0/24 network.
3) All other traffic originating from the 192.168.3.0 network should be denied.
Which set of ACL statements meets the stated requirements when they are applied to the Fa0/0 interface of router R2 in the inbound direction?
• access-list 101 deny ip any any
access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255
• access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255
access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255
• access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255
• access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.2.0 0.0.0.255
access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.1.0 0.0.0.255
access-list 101 permit ip any any
• access-list 101 deny ip 192.168.3.77 0.0.0.0 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.3.0 0.0.0.255 192.168.0.0 0.0.255.255
15.
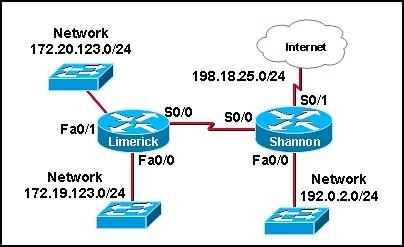
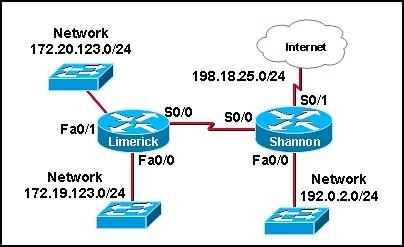
Hosts from the Limerick LAN are not allowed access to the Shannon LAN but should be able to access the Internet. Which set of commands will create a standard ACL that will apply to traffic on the Shannon router interface Fa0/0 implementing this security?
• access-list 42 deny 172.19.123.0 0.0.0.255 192.0.2.0 0.0.0.255
access-list 42 permit any
• access-list 56 deny 172.19.123.0 0.0.0.255
access-list 56 permit any
• access-list 61 deny 172.19.123.0 0.0.0.0
access-list 61 permit any
• access-list 87 deny ip any 192.0.2.0 0.0.0.255
access-list 87 permit ip any
16.
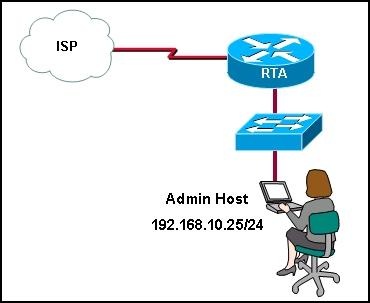
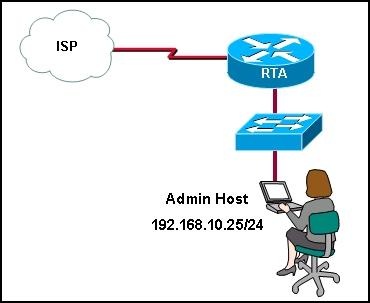
Refer to the exhibit. A network administrator needs to configure an access list that will allow the management host with an IP address of 192.168.10.25/24 to be the only host to remotely access and configure router RTA. All vty and enable passwords are configured on the router. Which group of commands will accomplish this task?
• Router(config)# access-list 101 permit tcp any 192.168.10.25 0.0.0.0 eq telnet
Router(config)# access-list 101 deny ip any any
Router(config)# int s0/0
Router(config-if)# ip access-group 101 in
Router(config-if)# int fa0/0
Router(config-if)#ip access-group 101 in
• Router(config)# access-list 10 permit 192.168.10.25 eq telnet
Router(config)# access-list 10 deny any
Router(config)# line vty 0 4
Router(config-line)#access-group 10 in
• Router(config)# access-list 86 permit host 192.168.10.25
Router(config)# line vty 0 4
Router(config-line)# access-class 86 in
• Router(config)# access-list 125 permit tcp 192.168.10.25 any eq telnet
Router(config)# access-list 125 deny ip any any
Router(config)# int s0/0
Router(config-if)# ip access-group 125 in
17. Which ACL permits host 10.220.158.10 access to the web server 192.168.3.244?
• access-list 101 permit tcp host 10.220.158.10 eq 80 host 192.168.3.224
• access-list 101 permit tcp 10.220.158.10 0.0.0.0 host 192.168.3.224 0.0.0.0 eq 80
• access-list 101 permit host 10.220.158.10 0.0.0.0 host 192.168.3.224 0.0.0.0 eq 80
• access-list 101 permit tcp 10.220.158.10 0.0.0.0 host 192.168.3.224 eq 80
18. Which wildcard mask would match the host range for the subnet 192.16.5.32 /27?
• 0.0.0.32
• 0.0.0.63
• 0.0.63.255
• 0.0.0.31
19. A security administrator wants to secure password exchanges on the vty lines on all routers in the enterprise. What option should be implemented to ensure that passwords are not sent in clear text across the public network?
• Use Telnet with an authentication server to ensure effective authentication.
• Apply an access list on the router interfaces to allow only authorized computers.
• Apply an access list on the vty line to allow only authorized computers.
• Use only Secure Shell (SSH) on the vty lines.
20.
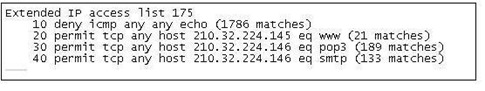
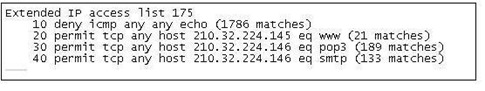
Refer to the exhibit. An administrator notes a significant increase in the amount of traffic entering the network from the ISP. The administrator clears the access-list counters. After a few minutes, the administrator again checks the access-list table. What can be concluded from the most recent output shown?
• A small amount of HTTP trafic is an indication that the web server was not configured correctly.
• A larger amount of POP3 traffic (compared with SMTP traffic) indicates that there are more POP3 email clients than SMTP clients in the enterprise.
• A large amount of ICMP traffic is being denied at the interface, which can be an indication of a DoS attack.
• A larger amount of email traffic (compared with web traffic) is an indication that attackers mainly targeted the email server.
CCNA Discovery 3 Module 6 Exam Answers Version 4.0
1.
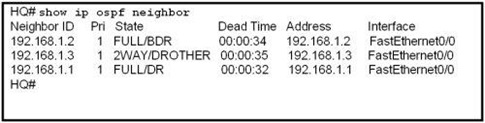
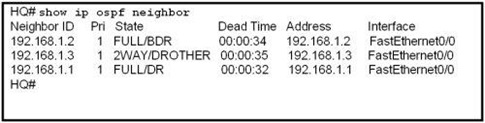
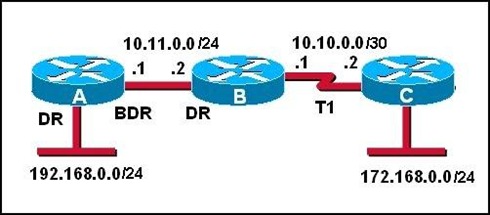
Refer to the exhibit. What statement describes the DR/BDR relationship of the HQ router?
• HQ is the DR.
• HQ is the BDR.
• HQ is a DROTHER.
• HQ is a member of an NBMA network.
2. Which two features are associated with Frame Relay OSPF point-to-multipoint environments? (Choose two.)
• A DR is not elected.
• The OSPF priority value determines the active DR on the Frame Relay link.
• OSPF neighbor routers are statically defined.
• The link types are identified as broadcast multiaccess.
• The BDR will have a router ID whose value is greater than the DR router ID.
3.
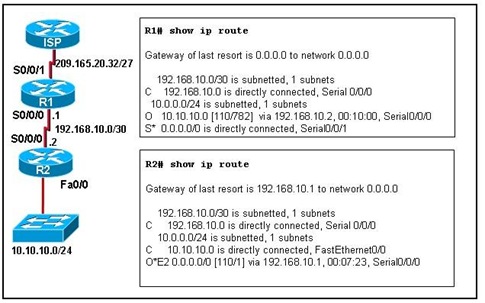
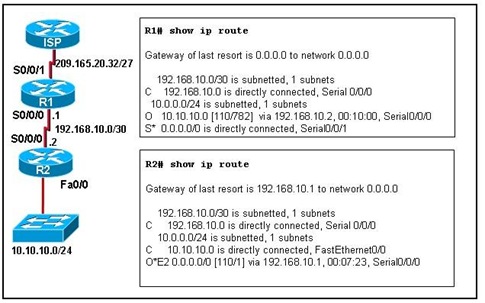
Refer to the exhibit. How was the OSPF default gateway entry for R2 determined?
• Default routes are automatically injected by OSPF into all advertisements.
• A static default gateway route is defined in the configuration of R2.
• The default-information originate command is applied on R1.
• The ISP defines the gateway of last resort and automatically passes it to R1 and R2.
• The ip default-gateway command is applied on R2.
4. What is always required for OSPF routers to share routing information?
• designated routers
• a backup designated router
• neighbor adjacencies
• an NBMA network topology
• links that are configured on the 224.0.0.0 network
5.
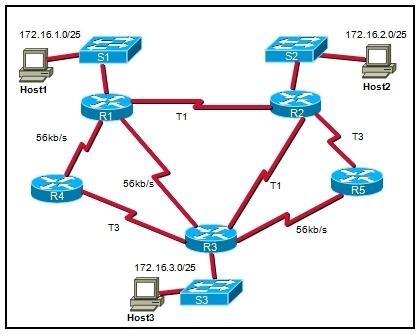
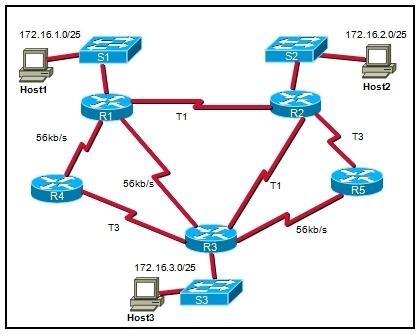
Refer to the exhibit. A network administrator has implemented OSPF and the network has converged. If all router interfaces are enabled and functional, what route will OSPF view as lowest cost when moving frames from Host3 to Host1?
• R3 to R4 to R1
• R3 to R1
• R3 to R2 to R1
• R3 to R5 to R2 to R1
6.
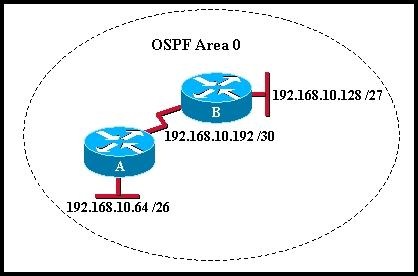
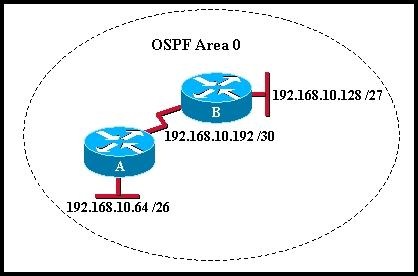
Refer to the exhibit. Which commands configure router A for OSPF?
• router ospf 1
network 192.168.10.0
• router ospf 1
network 192.168.10.64 0.0.0.63 area 0
network 192.168.10.192 0.0.0.3 area 0
• router ospf 1
network 192.168.10.64 255.255.255.192
network 192.168.10.192 255.255.255.252
• router ospf 1
network 192.168.10.0 area 0
7.
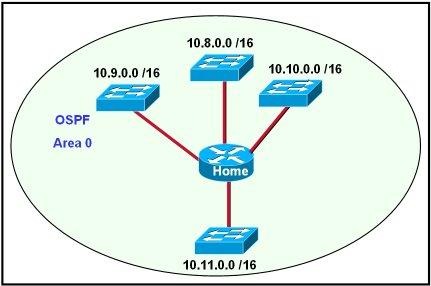
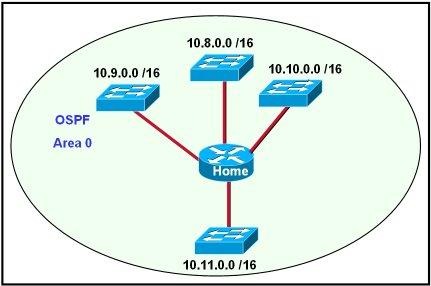
Refer to the exhibit. Which network statement configures the home router to allow all the interfaces to participate in OSPF?
• network 10.0.0.0 0.3.255.255 area 0
• network 10.8.0.0 0.0.0.3 area 0
• network 10.8.0.0 0.3.255.255 area 0
• network 10.10.0.0 0.0.0.3 area 0
• network 10.12.0.0 0.3.255.255 area 0
8. Which statement is true regarding OSPF DR and BDR elections?
• A new DR/BDR election occurs each time a new OSPF neighbor is added.
• The router with the highest OSPF priority setting wins the election for DR.
• The default priority value for a router connected to a multi-access network is 0.
• The router with the highest MAC address is elected as the DR when the default priority values are used.
9.

Refer to the exhibit. The network administrator would like only the 172.16.32.0 network advertised to Router1. Which OSPF network command accomplishes this?
• Router2(config-router)# network 172.16.0.0 0.0.0.15 area 0
• Router2(config-router)# network 172.16.0.0 0.0.15.255 area 0
• Router2(config-router)# network 172.16.32.0 0.0.15.255 area 0
• Router2(config-router)# network 172.16.32.0 0.0.255.255 area 0
10. Which two statements describe the operation of link-state routing protocols? (Choose two.)
• All routers in the same area have identical link-state databases when converged.
• Routing loops are prevented by running the Diffusing Update Algorithm (DUAL).
• Link-state routers send frequent periodic updates of the entire routing table.
• Reliable Transport Protocol (RTP) is used to deliver and receive LSAs.
• Calculating the shortest path for each destination is accomplished with the SPF algorithm.
11.
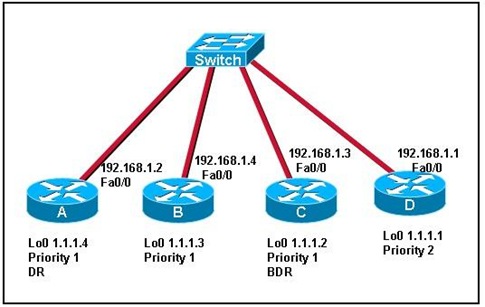
Refer to the exhibit. Routers A, B, and C are part of the existing OSPF network. Router D has been added to the network. All routers are running OSPF and have the indicated priorities applied to the interface. What is the DR/BDR status immediately after router D is added to the existing network?
• An election is forced and router D wins the DR election.
• The DR and BDR do not change until the next election.
• An election is forced and the existing BDR becomes the DR.
• The router with the highest router ID becomes the new BDR.
12. Which two statements describe the use of OSPF DR/BDR elections? (Choose two.)
• Elections are always optional.
• Elections are required in all WAN networks.
• Elections are required in point-to-point networks.
• Elections are required in broadcast multiaccess networks.
• Elections are sometimes required in NBMA networks.
13.
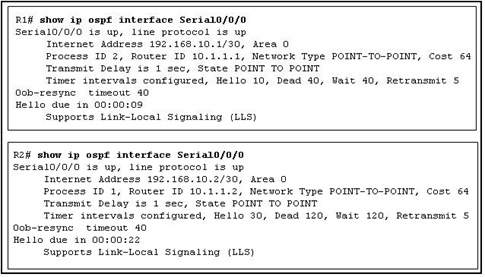
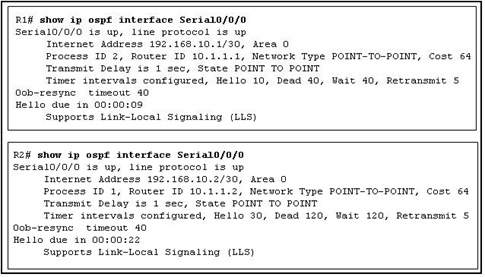
Refer to the exhibit. As part of an OSPF network, R1 and R2 are trying to become adjacent neighbors. Although it appears that the two systems are communicating, neither of the routing tables include OSPF routes received from its neighbor. What could be responsible for this situation?
• R1 and R2 are not on the same subnet.
• The Process IDs on each router do not match.
• The timer intervals on the routers do not match.
• The value set for the Transmit Delay time on both routers is too low.
14.
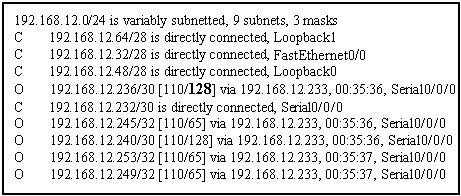
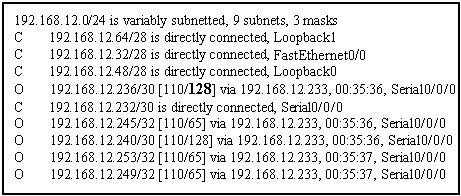
Refer to the exhibit. What is the purpose of the value 128 shown in bold?
• It is the OSPF cost metric.
• It is the OSPF administrative distance.
• It is the value assigned by the Dijkstra algorithm that designates the distance in hops to the network.
• It is the value assigned to an interface that is used by the DUAL algorithm to determine the metric.
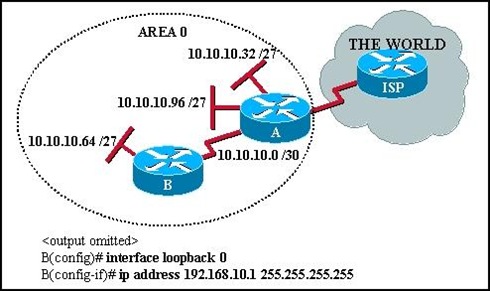
15.
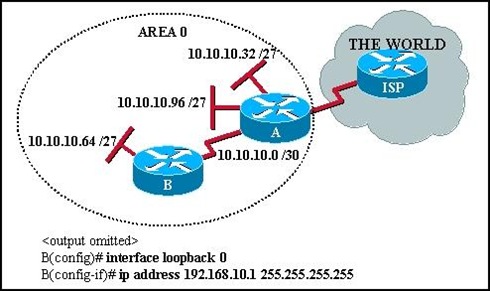
Refer to the exhibit. What is the purpose of the configuration commands added on router B?
• allows router A to form an adjacency with router B
• provides a stable OSPF router ID on router B
• provides a method of testing router traffic
• creates the OSPF adjacency table on router B
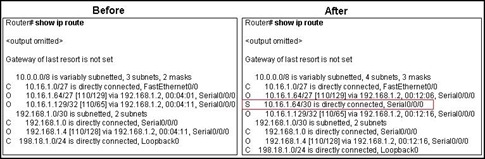
16.
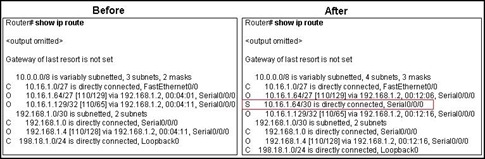
Refer to the exhibit. The command ip route 10.16.1.64 255.255.255.252 s0/0/0 is entered into the router. Why does network 10.16.1.64/30 appear in the routing table in addition to network 10.16.1.64/27?
• The router views 10.16.1.64/30 and 10.16.1.64/27 as two different networks.
• The static route is used as a backup route for packets destined for 10.16.1.64/27.
• The AD for static routes is lower than the AD for OSPF routes.
• The static route metric is lower than the OSPF metric for the 10.16.1.64/27 network.
17. What is the primary difference between link-state protocols and distance vector protocols with regard to route calculation?
• Distance vector protocols take existing routes from their neighbors and add to them. Link-state protocols independently calculate full routes.
• Link-state protocols calculate and pass full routing tables to all routers in their associated areas, and distance vector protocols do not.
• When determining invalid routes, link-state protocols use split horizon for all route computations. Distance vector protocols use reverse poisoning.
• Distance vector protocols require more CPU and RAM for route calculations than link-state protocols require.
18. What range of networks are advertised in the OSPF updates by the command Router1(config-router)# network 192.168.0.0 0.0.15.255 area 0?
• 192.168.0.0/24 through 192.168.0.15/24
• 192.168.0.0/24 through 192.168.15.0/24
• 192.168.15.0/24 through 192.168.31.0/24
• 192.168.15.0/24 through 192.168.255.0/24
• 192.168.16.0/24 through 192.168.255.0/24
19.
Refer to the exhibit. When establishing adjacency relationships, which IP address would router A use to send hello packets to router B?
• 10.11.0.1
• 10.11.0.2
• 10.11.0.255
• 224.0.0.5
• 255.255.255.255
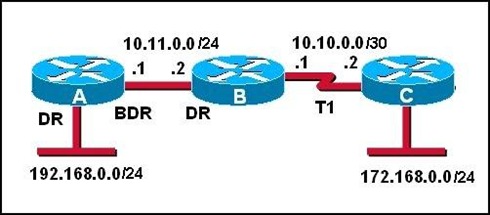
20.
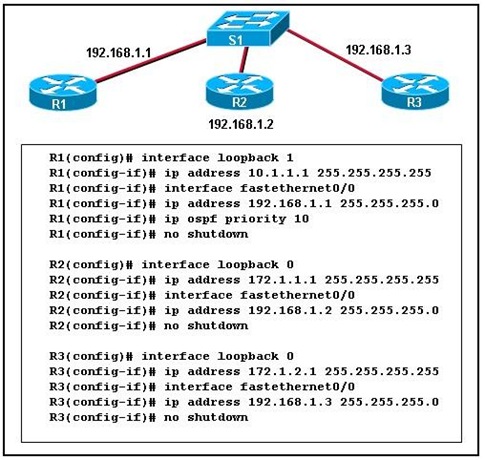
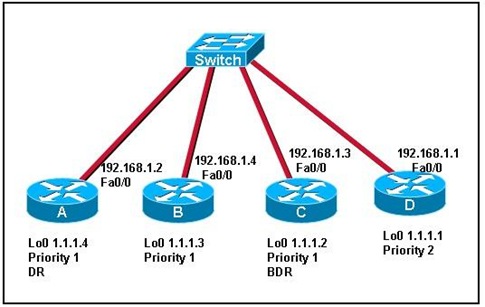
Refer to the exhibit. Which router will be elected the DR and which will become the BDR?
• R1 will be DR and R2 will be BDR.
• R1 will be DR and R3 will be BDR.
• R2 will be DR and R1 will be BDR.
• R2 will be DR and R3 will be BDR.
• R3 will be DR and R2 will be BDR.
• R3 will be DR and R1 will be BDR.
21. When compared to a distance vector routing protocol, what is a benefit of the hierarchical design approach that is used in large OSPF networks?
• simpler configuration
• reduction of router processing requirements
• isolation of network instability
• less complex network planning
22. What are two advantages of using a link-state routing protocol instead of a distance vector routing protocol? (Choose two.)
• The topology database eliminates the need for a routing table.
• Frequent periodic updates are sent to minimize the number of incorrect routes in the topological database.
• Routers have direct knowledge of all links in the network and how they are connected.
• After the initial LSA flooding, routers generally require less bandwidth to communicate changes in a topology.
• A link-state routing protocol requires less router processor power.
23. If a network has converged, what is true about the link-state database held by each router in the same OSPF area?
• Each router has a link-state database containing the same status information.
• Each router has a different link-state database depending on its position within the network.
• The link-state database is stored in a designated router and is accessed by each router in the area as needed.
• The link-state database in each router only contains information about adjacent routers and the status of their links.
24.
Refer to the exhibit. RTRC was recently configured and is not sending the proper OSPF routes to RTRB, as shown in the RTRB routing table. Based on the RTRC configuration, what is most likely the problem?
• RTRC interfaces are administratively shut down.
• The OSPF process ID for RTRC does not match the process ID used on RTRB.
• The interface addresses on RTRC overlap with other addresses in the network.
• The OSPF routing configuration on RTRC has a missing or incorrect network statement.